Which Of The Following Personally Owned Peripherals Can You Use
Holbox
Mar 31, 2025 · 6 min read
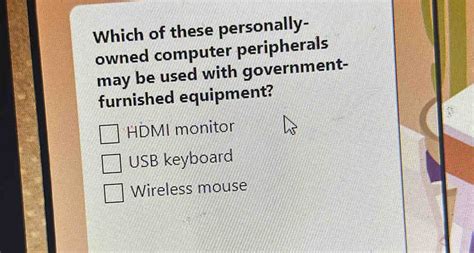
Table of Contents
- Which Of The Following Personally Owned Peripherals Can You Use
- Table of Contents
- Which of Your Personally Owned Peripherals Can You Use at Work? A Comprehensive Guide
- Understanding Your Company's IT Policy
- Peripherals Commonly Used: A Case-by-Case Analysis
- Best Practices for Using Personally Owned Peripherals
- The Importance of Understanding Legal and Ethical Considerations
- Conclusion
- Latest Posts
- Latest Posts
- Related Post
Which of Your Personally Owned Peripherals Can You Use at Work? A Comprehensive Guide
The line between personal and professional technology blurs increasingly in today's interconnected world. Many of us comfortably use our own smartphones, headphones, and even keyboards at work, but the rules surrounding acceptable personal technology usage vary wildly depending on your employer, industry, and even your role within the company. This guide explores the nuanced landscape of personally owned peripherals in the workplace, offering insights to help you navigate this complex area and ensure compliance while maximizing productivity and convenience.
Understanding Your Company's IT Policy
Before even considering plugging in your favorite noise-canceling headphones, thoroughly review your company's IT policy. This document is the ultimate authority on acceptable technology use, outlining what's allowed, restricted, or strictly prohibited. Often buried deep within employee handbooks or on internal portals, this policy is crucial for avoiding accidental violations and potential disciplinary action. Look for sections specifically addressing:
- BYOD (Bring Your Own Device) policies: These policies specifically address the use of personal devices, including peripherals, in the workplace. They might detail security protocols, acceptable use guidelines, and responsibilities regarding data protection.
- Acceptable Use of IT Resources: While not always explicitly focused on personal devices, this section usually covers general standards for acceptable computer use, often including guidelines on data security, internet usage, and appropriate software.
- Data Security and Confidentiality: Your company will likely have robust protocols to protect sensitive data. This includes restrictions on external storage devices, unapproved software, and the transfer of information between personal and company devices.
Ignoring your company's IT policy can have severe consequences, ranging from warnings and reprimands to termination of employment. Understanding the rules is the first and most critical step in responsibly using personal peripherals at work.
Peripherals Commonly Used: A Case-by-Case Analysis
Let's examine some commonly used personally owned peripherals and analyze the potential issues related to their workplace use:
1. Headphones/Earbuds: These are perhaps the most widely accepted personally owned peripherals. Many workplaces understand the need for focused work environments and the benefits of noise reduction. However, even headphones have potential issues:
- Security: If you connect your headphones to your work computer to access company networks, you are increasing your company's vulnerability to malware and unauthorized access. Your headphones might have pre-installed software or configurations that could compromise security.
- Sound Quality and Privacy: Certain headphones might leak audio, compromising confidential conversations or data. Consider the sound quality and your colleagues' work environments. Open-ear headphones, for instance, might be disruptive.
- Company-Provided Alternatives: Some companies provide headphones or headsets for specific tasks, like customer service calls. Check if such alternatives exist before using your own.
2. Keyboards and Mice: Ergonomics are a significant workplace concern, and using your preferred keyboard and mouse can significantly improve comfort and productivity. However, consider:
- Compatibility: Ensure your personal keyboard and mouse are compatible with your company's operating system and software. Driver issues can hinder productivity.
- Security Risks: Similar to headphones, connecting external devices increases the potential entry points for malicious software. Avoid using devices that haven’t been properly sanitized and updated.
- Company Provided Equipment: Again, check whether the company provides ergonomic keyboards and mice. Using your own might void any warranty on company-provided equipment.
3. External Hard Drives and USB Drives: These are generally considered high-risk peripherals due to the potential for data breaches and malware. Most companies strictly restrict or completely prohibit their use on company computers.
- Data Security: External drives can easily carry malware and expose sensitive company data to unauthorized access or theft.
- Data Loss: Loss or damage to the external drive can result in significant data loss for both personal and company files.
- Unauthorized Software: External drives might contain unauthorized software, potentially violating company policy and causing security vulnerabilities.
4. Webcams and Microphones: These peripherals are commonly used for video conferencing and collaboration. However, their use at work requires careful consideration:
- Privacy: Your webcam and microphone transmit images and sounds, raising significant privacy concerns, especially if used in company spaces. Ensure you are aware of any potential surveillance or recording policies.
- Security: Similar to other peripherals, these devices could become entry points for malicious software.
- Company-Provided Equipment: Many companies provide dedicated video conferencing equipment for security and compatibility reasons. Check if such tools are available.
5. Printers and Scanners: Usually, companies provide shared printing and scanning facilities. Using your own could lead to various issues:
- Network Security: Connecting a personal printer to the company network poses significant security risks.
- Compatibility Issues: Your personal printer might not be compatible with the company's network or software.
- Maintenance and Support: The company might not provide support for personal printers.
6. Mobile Phones: The use of mobile phones in the workplace is a complex issue often addressed by separate BYOD policies. While using your phone for personal calls and texts might be acceptable during breaks, accessing work-related data or using it for work communication often requires careful consideration and adherence to the company's specific mobile device policy. This commonly includes restrictions on specific apps, network access, and data encryption.
Best Practices for Using Personally Owned Peripherals
Regardless of your company's policy, adhering to best practices minimizes risks and ensures a smooth workflow:
- Always obtain permission: Before using any personal peripheral, explicitly seek permission from your IT department or manager.
- Regularly update software: Keep your peripherals' software updated to patch security vulnerabilities.
- Use strong passwords: Protect your devices with robust passwords and multi-factor authentication if available.
- Avoid sharing devices: Refrain from sharing your personal devices with colleagues to minimize security risks.
- Back up your data: Regularly back up important data to prevent loss.
- Practice good data hygiene: Be mindful of the data you transfer between personal and company devices.
- Keep your peripherals clean: Regularly clean your devices to maintain hygiene and prevent the spread of germs.
- Understand your company's acceptable use policy: Regularly review and familiarize yourself with the company's IT policies.
The Importance of Understanding Legal and Ethical Considerations
Beyond company policies, consider legal and ethical considerations. Using personally owned peripherals might inadvertently expose your company to legal liability if it violates data privacy regulations like GDPR or CCPA. Ensure your actions comply with all relevant laws and regulations. Ethical considerations also play a critical role. Respecting colleagues' privacy and avoiding actions that could negatively affect the work environment are vital.
Conclusion
Navigating the use of personally owned peripherals at work requires careful planning and awareness. Prioritize understanding your company's IT policy, identify potential risks, and follow best practices to ensure compliance, security, and efficient productivity. Remember that the convenience of using personal devices needs to be balanced against the potential risks to company security and data integrity. By proactively addressing these concerns, you can confidently integrate personal technology into your professional life while mitigating potential issues. Always remember to prioritize your company's data security and well-being as your actions reflect not only on you but also on your employer. Regularly checking for updates to your company's policies is also vital to stay informed and compliant.
Latest Posts
Latest Posts
-
The Distinction Between Impulse And Force Involves The
Apr 04, 2025
-
Which Of The Following Is True Of The
Apr 04, 2025
-
Your Restaurants Fish Delivery Just Arrived
Apr 04, 2025
-
Turbine Blades Mounted To A Rotating Disc
Apr 04, 2025
-
Identify The Type Of Surface Represented By The Given Equation
Apr 04, 2025
Related Post
Thank you for visiting our website which covers about Which Of The Following Personally Owned Peripherals Can You Use . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.
