Who Do Legitimate Sharepoint Documents Come From
Holbox
Mar 31, 2025 · 5 min read
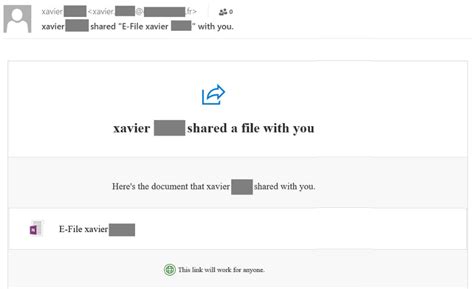
Table of Contents
- Who Do Legitimate Sharepoint Documents Come From
- Table of Contents
- Who Do Legitimate SharePoint Documents Come From? Ensuring Document Authenticity in Your Organization
- Understanding the SharePoint Ecosystem: Internal and External Sources
- 1. Internal Users: The Backbone of Your Document Library
- 2. External Users: Carefully Managed Access
- 3. Automated Systems and Integrations: A Growing Source of Data
- Red Flags: Identifying Potentially Suspicious Documents
- Strategies for Ensuring Document Authenticity
- 1. Robust Access Control and Permissions: The Foundation of Security
- 2. Enforce Strong Password Policies and Multi-Factor Authentication (MFA)
- 3. Data Loss Prevention (DLP) and Information Rights Management (IRM): Protecting Sensitive Information
- 4. Regular Security Audits and Vulnerability Assessments: Proactive Security Measures
- 5. User Training and Awareness: Empowering Your Workforce
- 6. Document Version Control and Audit Trails: Maintaining a Clear History
- 7. Establish Clear Naming Conventions and Metadata Standards: Ensuring Consistency and Searchability
- 8. Secure External Collaboration: Protecting Against External Threats
- Conclusion: A Proactive Approach to SharePoint Security
- Latest Posts
- Latest Posts
- Related Post
Who Do Legitimate SharePoint Documents Come From? Ensuring Document Authenticity in Your Organization
SharePoint, a widely-used platform for document management and collaboration, offers significant advantages for businesses of all sizes. However, its very accessibility introduces the crucial question: who do legitimate SharePoint documents actually come from? Understanding the source of your documents is paramount for maintaining data integrity, security, and the overall trust within your organization. This comprehensive guide delves into identifying trustworthy SharePoint document sources, highlighting potential red flags and outlining strategies for securing your digital assets.
Understanding the SharePoint Ecosystem: Internal and External Sources
Before we explore identifying legitimate documents, let's clarify the potential sources within the SharePoint ecosystem. Documents can originate from:
1. Internal Users: The Backbone of Your Document Library
The majority of legitimate SharePoint documents should come from authorized internal users within your organization. These individuals are typically employees, contractors, or partners with established accounts and permissions within your SharePoint environment. Legitimate documents created by internal users should adhere to:
- Established Naming Conventions: Your organization likely has a naming convention for documents, ensuring consistency and easy searchability. Documents deviating from this standard should raise a flag.
- Version Control: SharePoint's version control feature is crucial. Legitimate documents usually have a clear version history, showing edits and modifications made over time by authorized personnel.
- Metadata Compliance: Documents should include appropriate metadata, such as author, date created, department, and keywords. Inconsistent or missing metadata may suggest an unauthorized source.
- Approval Workflow: Many organizations utilize approval workflows. Legitimate documents often show a clear approval trail, indicating they've been reviewed and authorized by relevant stakeholders.
2. External Users: Carefully Managed Access
SharePoint can also facilitate collaboration with external users, such as clients, vendors, or consultants. However, access for external users should be strictly controlled and monitored:
- Guest Accounts: External users typically access SharePoint through guest accounts with limited permissions, preventing unauthorized access to sensitive information. Documents from external users should be meticulously reviewed and validated.
- Secure Sharing Links: When sharing documents externally, use secure links that expire after a certain period or limit access to specific individuals.
- Data Loss Prevention (DLP) Policies: Implement DLP policies to prevent sensitive data from leaving your organization's control, even when shared with external users.
- Regular Audits: Regularly audit external user access and permissions to ensure only necessary individuals have the required access levels.
3. Automated Systems and Integrations: A Growing Source of Data
Increasingly, SharePoint integrates with various automated systems, including:
- CRM Systems: Data from your CRM can be automatically imported into SharePoint, creating reports and analyses.
- ERP Systems: Similarly, integration with ERP systems can generate reports and documents within SharePoint.
- Other Applications: Numerous applications offer integration with SharePoint, automatically populating documents or data.
While these integrations offer efficiency, it's crucial to:
- Validate Data Integrity: Verify the accuracy and reliability of data imported from automated systems.
- Monitor Data Sources: Keep track of which systems are integrating data into your SharePoint environment.
- Establish Authentication Protocols: Ensure secure authentication methods between SharePoint and external systems.
Red Flags: Identifying Potentially Suspicious Documents
Several red flags indicate a SharePoint document might not be legitimate:
- Suspicious File Names: Odd characters, unusual capitalization, or names that don't align with your organizational conventions.
- Unknown Authors: Documents from users without clear identities or who haven't been authorized to access the relevant SharePoint site.
- Unexpected Content: Documents containing irrelevant information, inappropriate language, or malicious code.
- Missing or Inconsistent Metadata: A lack of essential metadata, such as author or creation date, or inconsistencies within metadata fields.
- Unverified Sources: Documents originating from unknown or untrusted external sources.
- Suspicious Links: Documents containing links that redirect to unfamiliar websites or prompt for sensitive information.
- Unusual File Sizes: Extremely large or small file sizes compared to the expected content.
- Modified Dates that Don't Match Activity: A document showing a recent modification date but lacking any recent activity or edit history.
Strategies for Ensuring Document Authenticity
To strengthen the authenticity of your SharePoint documents, employ the following strategies:
1. Robust Access Control and Permissions: The Foundation of Security
Implement a granular access control system, assigning specific permissions to different users and groups based on their roles and responsibilities. Regularly review and update these permissions to ensure they remain appropriate.
2. Enforce Strong Password Policies and Multi-Factor Authentication (MFA)
Protect user accounts with strong password policies that include complexity requirements, length restrictions, and regular password changes. Implement MFA to add an extra layer of security, requiring users to authenticate through multiple channels.
3. Data Loss Prevention (DLP) and Information Rights Management (IRM): Protecting Sensitive Information
Utilize DLP and IRM features to control access to sensitive data within SharePoint. DLP monitors and prevents the transfer of confidential information, while IRM controls access, usage, and distribution of documents.
4. Regular Security Audits and Vulnerability Assessments: Proactive Security Measures
Regularly conduct security audits and vulnerability assessments to identify and address potential security weaknesses in your SharePoint environment. Stay updated on the latest security patches and updates.
5. User Training and Awareness: Empowering Your Workforce
Educate your users on security best practices, including recognizing phishing attempts, creating strong passwords, and identifying suspicious documents or emails. Regular security awareness training significantly reduces the risk of social engineering attacks.
6. Document Version Control and Audit Trails: Maintaining a Clear History
Leverage SharePoint's version control to track changes made to documents. Audit trails provide a record of user activity, enabling you to identify unauthorized access or modifications.
7. Establish Clear Naming Conventions and Metadata Standards: Ensuring Consistency and Searchability
Develop clear naming conventions and metadata standards for all documents within your SharePoint environment. This improves searchability and ensures consistency across your document library.
8. Secure External Collaboration: Protecting Against External Threats
When collaborating with external users, use secure sharing links with expiration dates and limited access. Regularly review external user access and permissions.
Conclusion: A Proactive Approach to SharePoint Security
Ensuring the authenticity of SharePoint documents requires a proactive and multi-faceted approach. By understanding the potential sources of documents, identifying red flags, and implementing robust security measures, you can maintain data integrity, protect sensitive information, and foster a trustworthy environment within your organization. Remember that security is an ongoing process—regular reviews, updates, and user training are vital to safeguarding your valuable data stored within SharePoint. A strong security posture not only protects your organization but also builds confidence and trust among your employees and collaborators. Investing in robust security practices ultimately leads to a more efficient and secure collaborative workflow.
Latest Posts
Latest Posts
-
Which Of The Following Are True About Outgroups
Apr 03, 2025
-
A Joint Venture Establishes A New Business That Is
Apr 03, 2025
-
A Hazardous Material Spill Occurred During Transportation
Apr 03, 2025
-
The Major Product Of This Reaction Exists As Two Stereoisomers
Apr 03, 2025
-
Introduction To Leadership Concepts And Practice
Apr 03, 2025
Related Post
Thank you for visiting our website which covers about Who Do Legitimate Sharepoint Documents Come From . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.
